Map Identity Provider Groups
Identity Provider Mapping (IdP Mapping) is about using a single trusted service (IdP) to manage users identities across multiple different applications or websites, simplifying the login process and enhancing security.
Key terminology
Identity Provider (IdP): This is a service that stores and verifies user identity information. Think of it as a trusted place where user identities are kept. For example, when you log into a website using your Google or Microsoft account, Google or Microsoft is acting as the IdP. Okta can also act as an IdP.
- Mapping: This refers to the process of matching or linking one set of identity data with another. In the context of IdP Mapping and C3 AI, the process involves linking or mapping the identity information from the IdP (like Google or Microsoft) to the identity information in your C3 AI applications.
- IdP groups: These are groups or categories of users managed by the IdP. An IdP like Okta, Google, Microsoft, or an organization's own identity service can categorize users into different groups based on their roles, departments, or any other criteria.
- Mapping IdP groups to C3 AI groups: The process mentioned here involves linking (or mapping) one or more groups from the IdP to the C3 AI group in the application.
- Mapping: This refers to the process of matching or linking one set of identity data with another. In the context of IdP Mapping and C3 AI, the process involves linking or mapping the identity information from the IdP (like Google or Microsoft) to the identity information in your C3 AI applications.
Automatic Addition of Users: Once this mapping is set up, any user who is a member of the specified IdP groups will automatically be given the privileges of the C3 AI group when they log into the application. This means they don't need to be manually added to the C3 AI group within the app; their membership in the relevant IdP group is sufficient to grant them these privileges.
IdP mapping, OAuth, OIDC, SAML, and Okta
At a high level, IdP mapping is related to protocols like OAuth, SAML, OIDC, and platforms like Okta. It works in tandem with standards like OAuth, OIDC, and SAML, and is integral to identity management services like Okta, allowing for efficient and secure user authentication and authorization across multiple applications and services.
Here's how they interact:
IdP Mapping, OAuth, and OIDC
OAuth is a standard for access delegation, used in granting access tokens to applications, allowing them to act on behalf of a user. It's widely used for authorization in many online services. Refer to the topic on OAuth for more information.
OpenID Connect (OIDC) builds on OAuth 2.0, adding an authentication layer. It enables clients to verify the identity of a user based on the authentication performed by an authorization server, as well as to obtain basic profile information about the user. Refer to the topic on OpenID Connect Authentication for more information about setting up OIDC in the C3 Agentic AI Platform.
Relation to IdP Mapping: In an OAuth/OIDC context, an IdP (like Google or Microsoft) can authenticate users and provide tokens that other applications can use to obtain certain information about the user. IdP mapping in this scenario would involve mapping the authenticated user's identity and roles (obtained using OAuth/OIDC) to specific roles and permissions within a service or application.
IdP mapping and SAML
SAML is an XML-based standard for exchanging authentication and authorization data between parties, particularly between an IdP and a service provider (SP). It's often used in enterprise scenarios for Single Sign-On (SSO) solutions. Refer to the topic on how to Authenticate Using SAML for more information.
Relation to IdP mapping: In SAML, an IdP can send assertions (statements about a user's identity and attributes) to a service provider. The service provider can then map these assertions to specific roles and permissions within their system, much like IdP mapping.
IdP mapping and Okta
Okta is an identity management service that provides user authentication and authorization services, often using standards like OAuth, OIDC, and SAML. It acts as an IdP and can integrate with various applications and services. Refer to the topic on OpenID Connect and Okta integration for more information.
Relation to IdP mapping: With Okta, organizations can manage user identities and group memberships centrally. When Okta is integrated with other applications, these applications can map Okta-managed groups and roles to corresponding roles within their own systems, enabling streamlined access management and SSO capabilities.
Below is a diagram that illustrates the process and components involved in IdP Mapping.
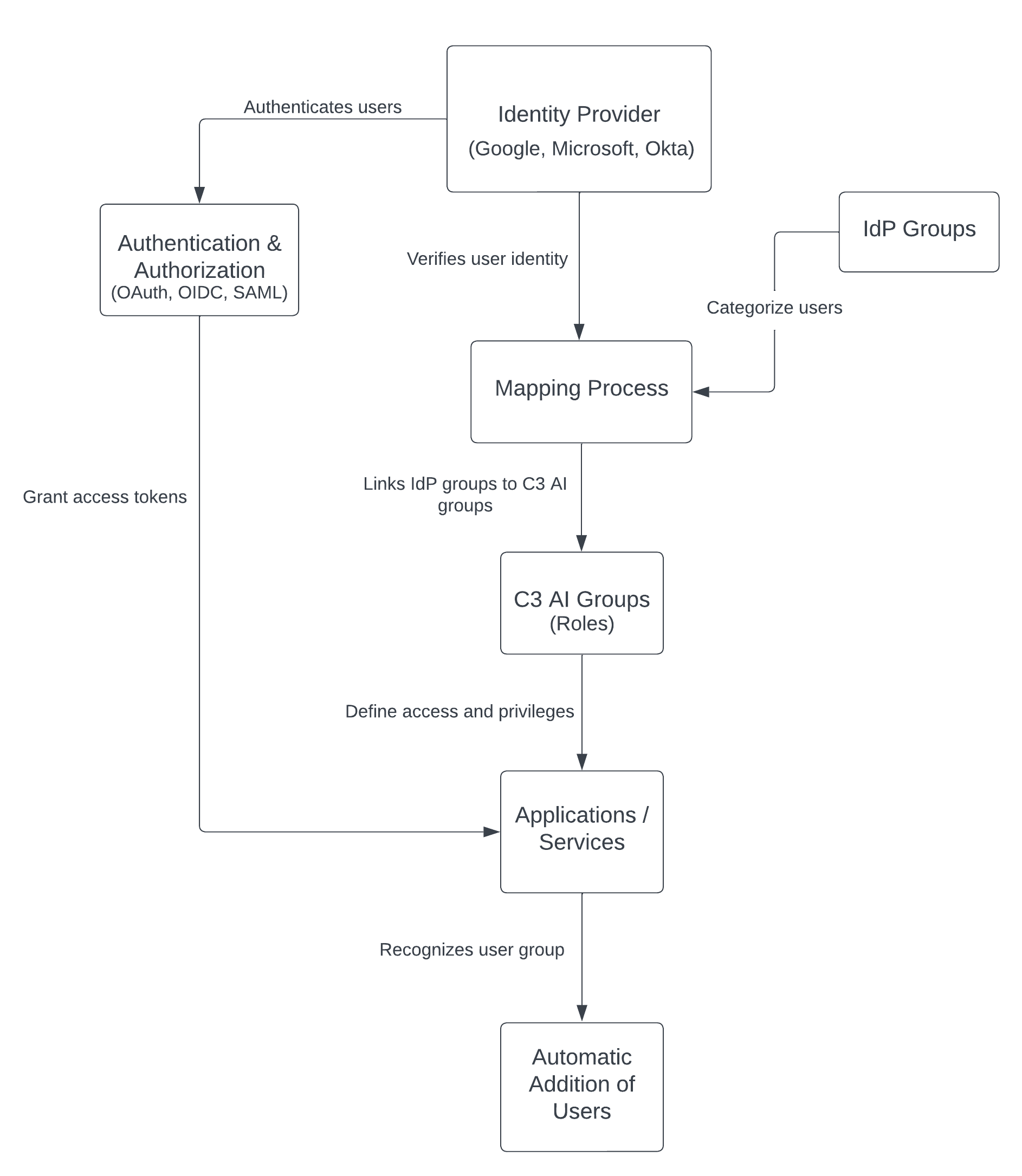
- Identity Provider (IdP): Represents services like Google, Microsoft, or Okta that store and verify user identity information.
- Mapping Process: The linkage between IdP groups and application-specific roles.
- Applications/Services: The target systems or applications where IdP mapping is applied.
- IdP Groups: Categories of users managed by the IdP.
- C3 AI Groups (or Application-Specific Roles): The roles within the application that IdP groups are mapped to.
- User Authentication and Authorization Flow: Including protocols like OAuth, OIDC, and SAML.
- Automatic Addition of Users: The process where users are automatically granted privileges based on their IdP group membership when they log into the application.
This diagram visually represents the IdP Mapping process. It starts with the IdP, which verifies user identities. These identities are then mapped through a specific process that links IdP groups to application-specific roles (C3 AI groups).
The applications or services define access and privileges based on these roles. The authentication and authorization flow, facilitated by protocols like OAuth, OIDC, and SAML, authenticates users and grants access tokens, allowing for the automatic addition of users to the appropriate groups within the applications based on their IdP group membership.
In the context of IdP Mapping, these protocols ensure that when you use your key(s), the system knows who you are, what doors you can open, and what you can do inside, all while keeping the process secure and streamlined.
C3 AI Studio user management
The C3 AI Studio user interface (UI) for setting up IdP Mapping only requires an application URL and a group name as input. The UI focuses on the essential information needed to establish a connection between the IdP like Okta and the application for the purpose of group-based access control.
Here's why each piece of information is crucial:
Application URL
- Purpose: The application URL uniquely identifies the specific application or service that the IdP will be interacting with. It acts as a destination where the IdP sends authentication responses, tokens, or SAML assertions after successfully authenticating a user. This URL is often used in the context of redirects after login, telling the IdP where to send the user once they've been authenticated.
- Use in Mapping: By specifying the application URL, you're effectively telling the IdP, "Here's where to apply the authentication and authorization rules we're setting up." It ensures that the authentication process is tied specifically to the intended application, facilitating secure and directed communication between the IdP and the application.
Group name
- Purpose: The group name specifies a particular group within the IdP, such as Okta, that contains a set of users. This group is used to manage access control, determining which users are allowed to access the application based on their group membership.
- Use in Mapping: When you provide a group name, you're defining which users (based on their group membership in the IdP) should be granted access to the application. The mapping process involves linking this group with specific roles or permissions within the application. This way, any user who is a member of the specified group in the IdP will automatically have the appropriate access rights in the application.
The process simplified
Application URL Input: Tells the IdP where the user should be sent after authentication. It's like specifying the exact door that a key (authentication token or SAML assertion) should open.
Group Name Input: Identifies which set of users (based on group membership in the IdP) are allowed to access the application. It's like creating a list of people who are allowed to use a specific key.
This streamlined approach simplifies the setup process for IdP Mapping by focusing on the minimal, yet essential, information required to establish secure and functional access control. It allows for:
- Easy Configuration: Administrators can set up access control without navigating through complex settings.
- Scalability: As organizations grow, new applications or services can be added by specifying their URLs and relevant group names.
- Security: Ensures that only authenticated users with the right group membership can access the application, enhancing overall security posture.
In essence, requiring just the application URL and group name as input makes the process of integrating an application with an IdP like Okta straightforward, focusing on the critical components of identity management and access control.